White Paper — Maturing Your Endpoint Security Strategy with Tanium
At Chuco, we work with Tanium customers and partners daily to ensure cyber security is a top priority. Through years of endpoint security experience, we’ve developed a deep understanding of what it takes to make organizations successful with Tanium endpoint products.
The Log4Shell Threat to Businesses — Not Out of the Woods Yet

The FTC means business when it comes to pushing organizations to patch Log4j promptly. Even if you’ve taken the initial steps to patch your systems, the problem is that Log4Shell is not your typical vulnerability. Log4j is not software from a single vendor. Read more about the Tanium advantage in surfacing and remediating Log4Shell.
Tanium Threat Response Alert Tuning: How to Reduce Security Event Noise and Prioritize Real Threats
Alert fatigue is a well known problem in cybersecurity. Many organizations are flooded with so many security notifications, they are at significant risk of missing actual threats. Tanium Threat Response gives organization threat hunting, security operations, and incident response teams the deep visibility to surface valuable security endpoint data and telemetry.
How to Identify Missing and Active Tanium Clients
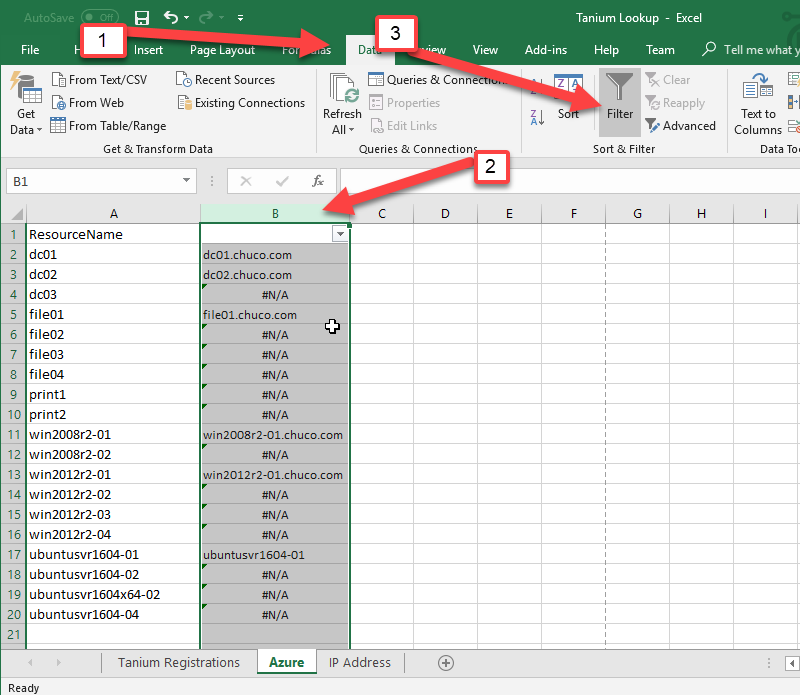
IntroductionThis document describes a process by which you can compare a list of host names generated from one or more sources against a list of systems currently managed by Tanium. Instead of manually searching Tanium System Status for individual machine names, you can utilize Microsoft Excel to perform the analysis and quickly extract a list […]
Tanium Release Spotlight – TanOS 1.3.x
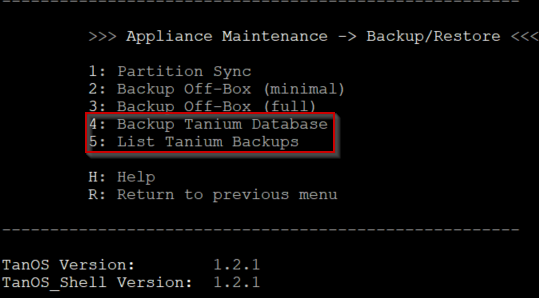
Introduction If you have not had the chance to use or see one of the Tanium appliances in action, you are missing out and I suggest you reach out to your TAM as soon as possible and inquire about them. Here at Chuco we are loving what Tanium is doing with this platform and how […]
How to use Maintenance and Reboot Tanium Solutions Lab Content to Create Policy-based Deployments
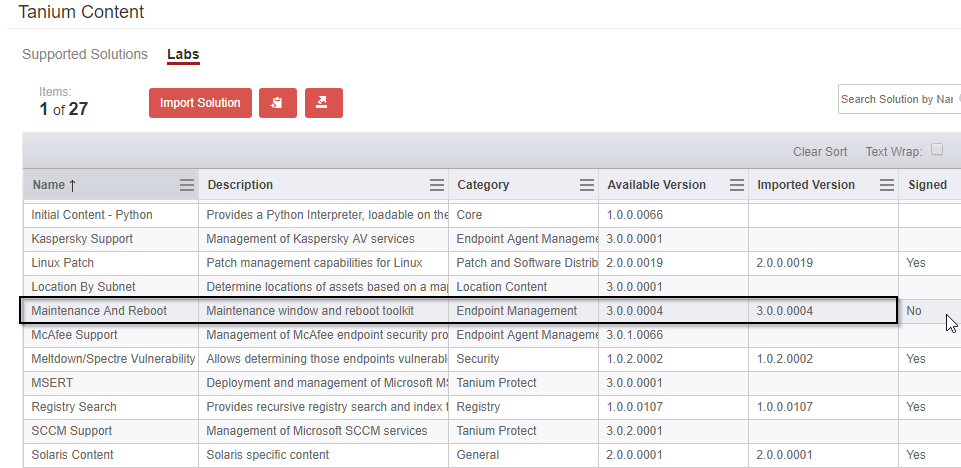
Deploying applications and module content can be challenging, especially when you need to work around 20 different change windows that depend on location, application, OS, system or server type (the list goes on). Here is an example of how you can use the Client Maintenance content in Tanium to help sift through all that without […]
How to Enable OS Fingerprinting in Tanium Discover
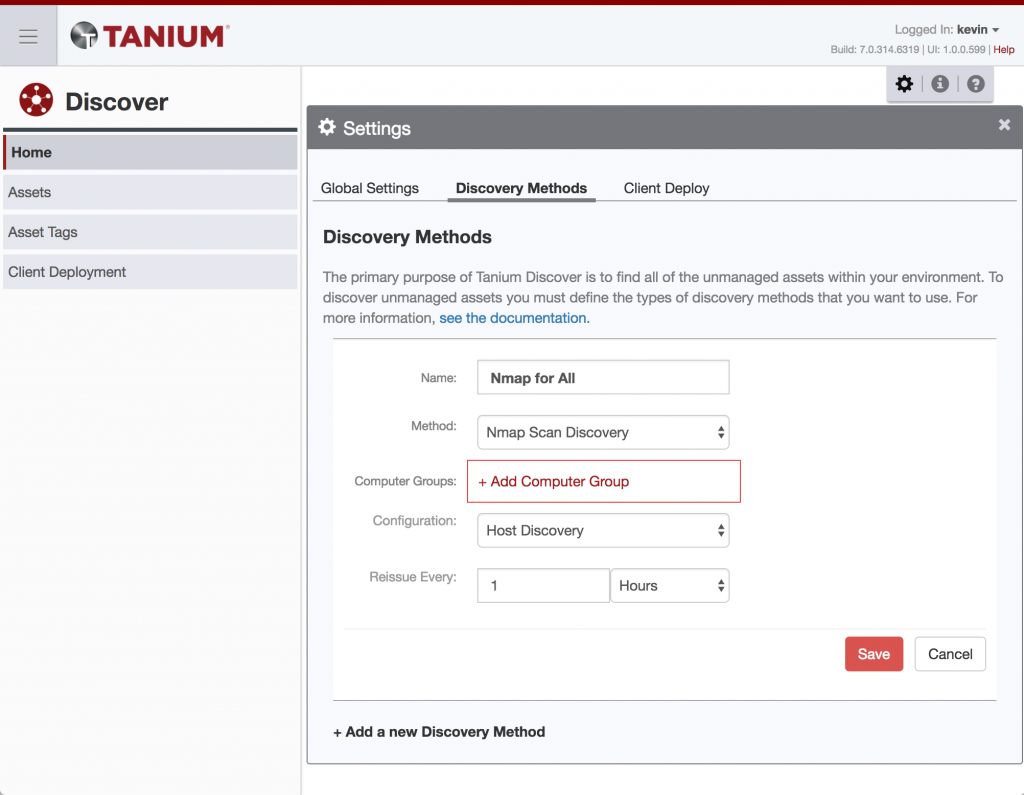
Normally this kind of configuration for a Tanium product module should be fairly straightforward, but I ran into a bug I hadn’t seen before, and spun my wheels for awhile. So — I figured I’d document this in case anyone else needed it. OS fingerprinting is one of the more interesting use cases for unmanaged […]
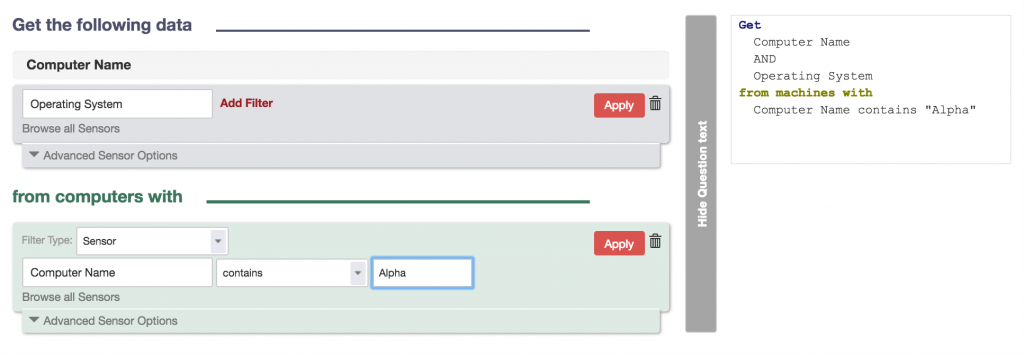
Quickstart on Using the Tanium Server SOAP API
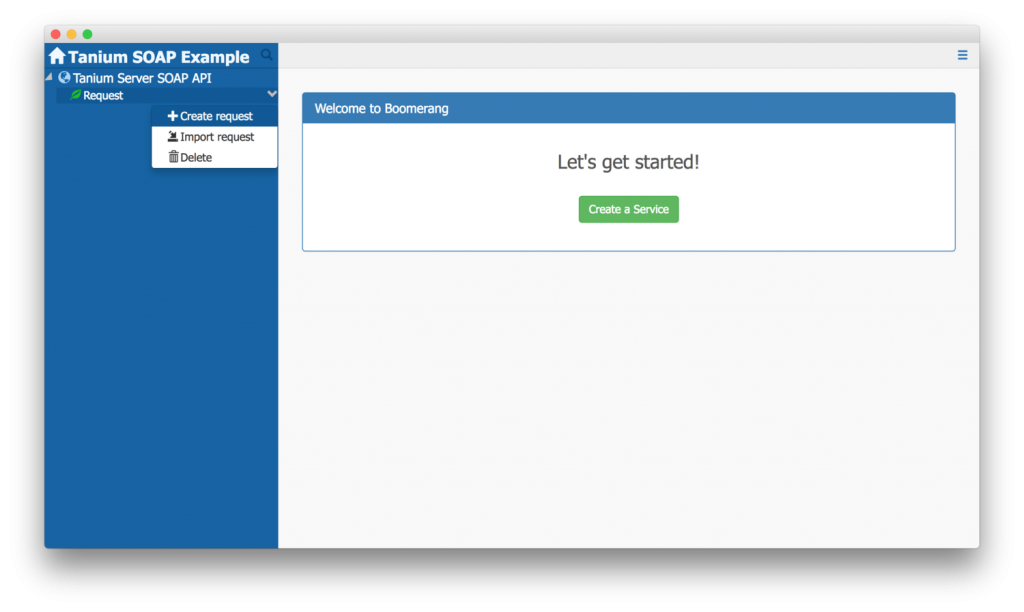
Here’s a short guide on how to get started with the Tanium Server SOAP API. This continues some of the discussion from the Integrations Through the Tanium Server API article and walks you through a quick way to immediately start playing with the Tanium Server API. Keep in mind that this doesn’t use the Pytan […]
Using Regular Expressions in Questions
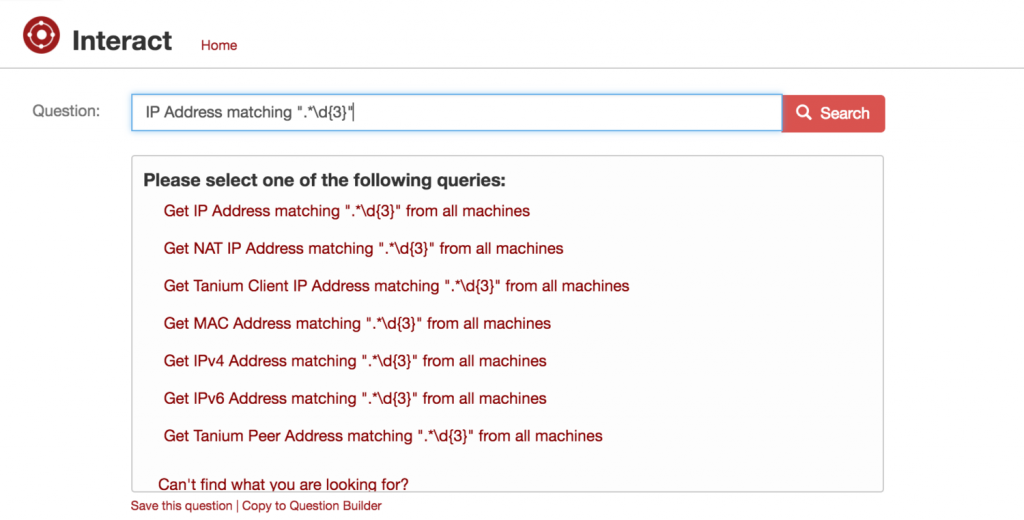
During a recent training, someone in the room was going through some hands-on training activities on how to ask Tanium Questions. As he was working through some Questions using some filters, he asked what a lot of others ask about: Can you use regular expressions in Questions? The answer to this insanely common question is […]
What is [no results] and How to Avoid It
Here’s a related follow up from Friday’s Basic Tips on Asking Questions article. In some cases you may run into “[no results]” when you’re first ramping up on how to use Tanium. In most cases, asking a Question with “[no results]” is perfectly harmless, but a lot of seasoned Tanium users will proclaim that its […]
